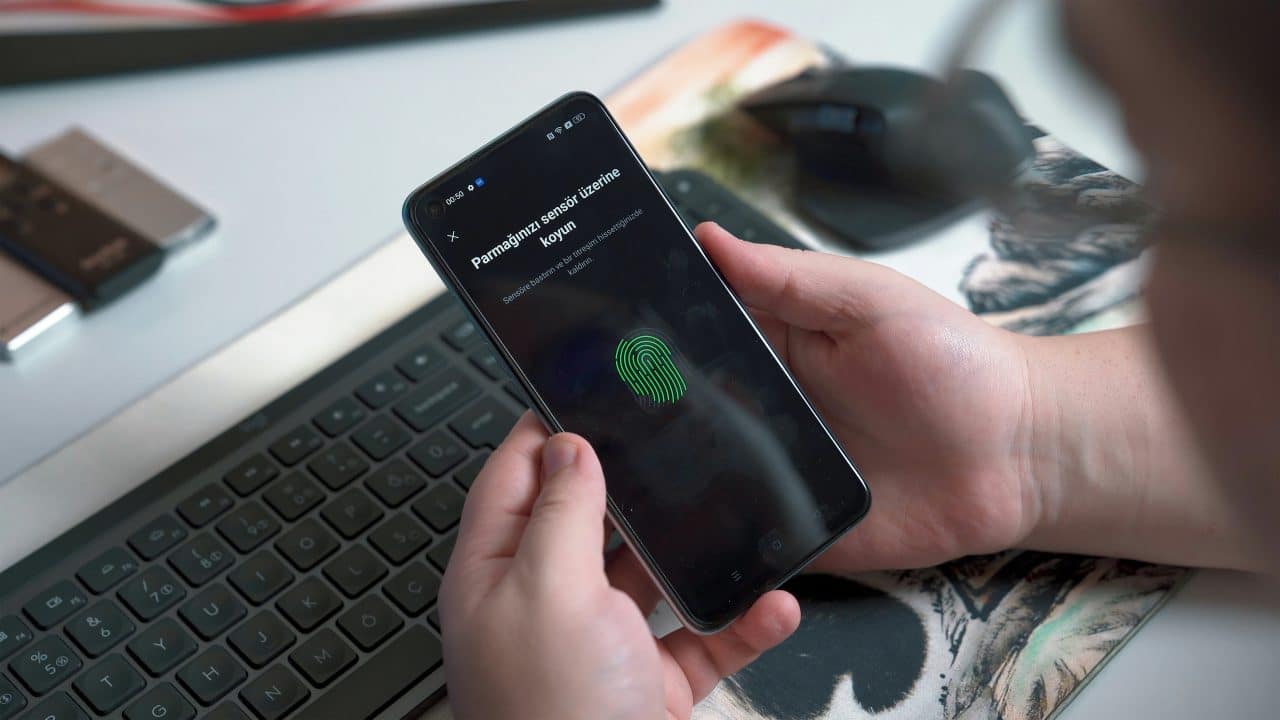
Biometric authentication methods like fingerprint, facial, and iris scanning are becoming increasingly commonplace.
According to Statista, about 80% of active mobile phones in North America, Western Europe, and Asia Pacific supported biometric features. Moreover, in 2022, about 46% of users in North America and Europe revealed that their organization had already enforced biometric technology due to its enhanced safety and user experience.
From unlocking your smartphone to passing through airport security to checking your bank balance, biometrics provide a convenient way to confirm your identity. But with this growing convenience come concerns and questions, especially for those who are new and are still understanding this ever-evolving world of technology.
If you have any misconceptions about how secure and foolproof these technologies are, you are in the right place. In this blog, we’ll debunk five common biometric myths about biometrics. This will help you make informed decisions about your and your family’s privacy.
Myth #1. Biometrics Are 100% Secure
While biometrics add an extra layer of security, no single method can be considered completely foolproof.
Fingerprint sensors have become very sophisticated, using AI to detect fake or spoofed prints. Spoofing is when someone tries to trick basic biometric systems. A determined hacker could create an artificial “gummy” finger from a mold to gain access. Contact lenses can also be designed to trick some iris scanning systems. Techniques like spoofing, using replicas such as high-resolution photos or 3D masks, can sometimes bypass these systems.
So, while spoofing biometrics is difficult, it’s not impossible. But you don’t need to panic. Top companies often use multifactor authentication, which combines biometrics with passwords or security codes. This, in turn, reduces the chances of someone hacking your device.
Remember, even the most sophisticated lock can be picked. However, layering your security makes it much harder for hackers to crack.
Myth #2. Hackers Can Access My Data as It’s Stored on the Cloud
Many people assume that using biometric authentication means their data is stored on the cloud and can be easily obtained by hackers. However, this is not true.
Reputable biometric services utilize encryption, decentralized storage, and other security measures to protect users’ data. In short, your biometric data isn’t stored as a single file in one location. Rather, the original file is replaced with something called a ‘biometric template’. This template contains all the unique, mathematically encoded characteristics of your image.
Now, this template is then further fragmented into smaller, encrypted pieces and stored in different locations. This makes it almost impossible for hackers to access it. And even if they do get their hands on it, without the right algorithm, they can’t decrypt the file. A perfect example would be Apple’s Face ID system.
Apple’s Face ID data is stored on a user’s local device on a Secure Enclave chip. Secure Enclave is a dedicated security subsystem integrated into their Apple Silicon (formerly known as A-series and M-series) chips. It is never uploaded to iCloud and is encrypted with a key only accessible to the Secure Enclave. Even if a cloud service is employed, biometric data is encrypted end-to-end and accessible only to authorized devices.
While no system is completely hack-proof, proper security protocols make it very difficult for hackers to access your biometric data from the cloud.
Myth #3. All Biometrics Are Equally Reliable
The belief that all biometric authentication methods offer the same level of reliability is a common misconception.
Each biometric method, be it fingerprint recognition, an iris scan, facial recognition, or voice recognition, possesses distinct strengths and weaknesses. There also exist significant differences in reliability and spoof resistance between them. Understanding these differences is crucial in selecting the appropriate modality for specific applications.
For example, according to Au10tix, fingerprints and iris scans remain the same over a lifetime, making them quite reliable. However, they are susceptible to spoofing with high-quality replicas. Whereas, iris scans, offer higher resistance to such tricks due to the unique patterns in your iris.
Facial recognition is also susceptible to changes in weight, age, or hairstyle. Voice recognition can be impacted by colds and flu. Moreover, behavioral biometrics like gait analysis are still emerging technologies. While all biometrics offer advantages, some identifiers, like fingerprints and iris scans, are far less prone to fluctuations and spoofing when properly implemented.
So, not all biometric options are 100% reliable. Remember, the “best” biometric depends on the specific application and security needs.
Myth #4. Law Enforcement Has Unfettered Access to Biometric Data
This is a complex issue with nuances, but the short answer is no!
Law enforcement doesn’t have unlimited access to your biometric data. Regulations and legal processes govern their access, varying depending on the specific data, situation, and location. For example, the Illinois Biometric Information Privacy Act (BIPA) passed in 2018, monitors the acquisition, handling, and usage of biometric data.
Under BIPA, companies must inform users, obtain consent, and put protections in place before collecting biometric data. Several tech giants, such as Facebook, Google, TikTok, and Snapchat, have already been penalized for violating BIPA regulations. The fines cost over $225 million, and various other lawsuits are still underway against major companies.
In general, law enforcement typically requires a warrant or subpoena to access biometric data held by private companies. Even government-collected data may have restricted access based on specific criteria. While concerns about law enforcement access are understandable, understanding the legal framework can provide some reassurance.
While there are gray areas, unfettered biometric data access by law enforcement remains illegal without proper legal authorization and oversight. Users maintain much of their privacy rights.
In conclusion, biometric authentication is a technology that has brought much convenience to our lives.
However, as with any new technology, there are common misunderstandings around its capabilities and security. While biometrics are highly secure, no solution is infallible. Being aware of the limitations allows us to use biometrics wisely — as a helpful addition to a multi-layered security strategy, not a magic bullet.
By staying informed about advancements, choosing reputable companies, and utilizing multifactor authentication, you empower yourself to make informed decisions about your biometric security. Stay informed, stay vigilant, and stay secure.
Buy Me A Coffee
The Havok Journal seeks to serve as a voice of the Veteran and First Responder communities through a focus on current affairs and articles of interest to the public in general, and the veteran community in particular. We strive to offer timely, current, and informative content, with the occasional piece focused on entertainment. We are continually expanding and striving to improve the readers’ experience.
© 2026 The Havok Journal
The Havok Journal welcomes re-posting of our original content as long as it is done in compliance with our Terms of Use.