Businesses rely on cameras to discourage theft, clarify what happened during an incident, and support safer day-to-day operations. The presence of visible cameras can change behavior, while recorded video can help resolve disputes, support internal investigations, and provide clear information to insurers or law enforcement when something goes wrong. That only works when the system stays available, trustworthy, and protected from simple interference like unplugging a device, blocking a lens, or cutting a cable.
Surveillance can fail in quiet, everyday ways, not just during major incidents. A camera angle can drift after a bump, a lens can collect dust, a recorder can run out of storage, or a shared password can spread farther than intended. When small issues pile up, the system may still look like it is working even though the footage is incomplete or unusable. Building reliability means anticipating these weak points and treating camera uptime and video integrity as part of normal operations.
Start With a Threat and Risk Picture
Begin by listing what could realistically go wrong at your site: vandalism, after-hours break-ins, internal theft, or a dispute where video might be needed. Match each risk to the locations and camera views that would help confirm events, not just show activity.
Next, decide what tampering would look like for you. Some attackers want to stop recording, while others want to degrade evidence by shaking a mount, spraying a lens, or forcing glare with a bright light.
Finally, document priorities. A loading dock camera that covers deliveries may be more critical than a hallway camera. This ranking helps you spend time and budget on the points that protect the operations you cannot afford to lose.
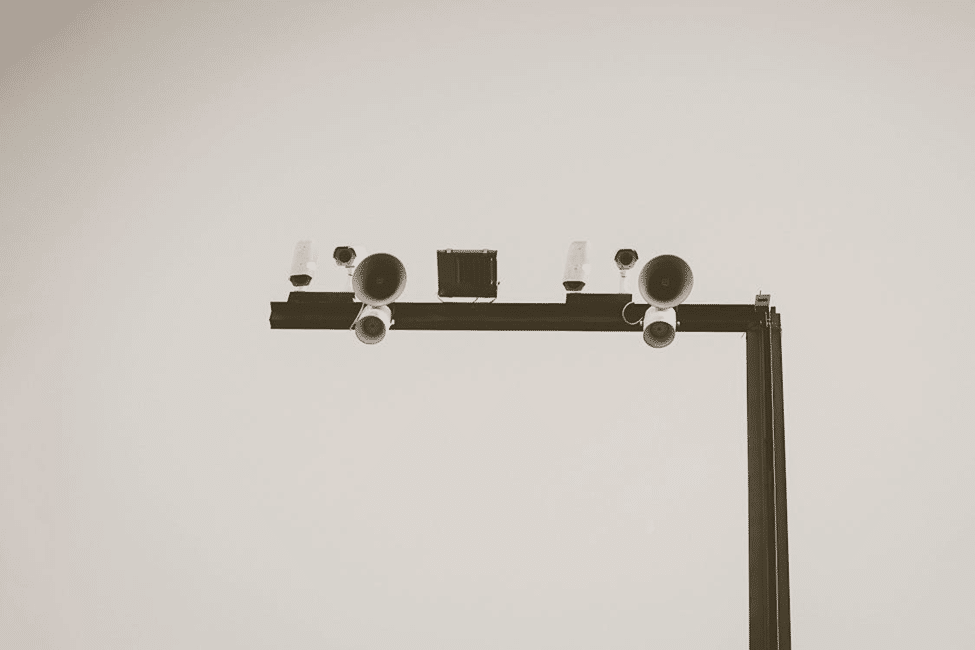
Build Security in Layers Around Cameras
A strong approach uses layers that deter, detect, and slow down interference. Physical security programs often describe this as security in depth, combining complementary controls rather than relying on one measure.
Start with layout choices: put key cameras higher, use protected conduit where cables are exposed, and avoid easy climbing routes near mounts. Pair cameras with lighting that supports clear images without creating harsh glare.
Add barriers where they make sense. Fencing, controlled gates, and designs that limit easy access to equipment reduce casual tampering and help staff notice suspicious behavior earlier.
Lock Down Access to Cameras and Video Recorders
Treat camera settings and recorder controls like you would treat financial systems. Limit who can change configurations, create accounts per person, and remove access when someone changes roles.
Use strong authentication and safer sign-in habits. NIST’s cybersecurity guidance encourages organized risk management and practical controls that reduce the chance of unauthorized access.
Protect the recorder or server physically. Place it in a locked room or cabinet, restrict keys, and keep a simple access log. If someone can walk up and pull a drive, your best camera coverage may not matter.
Harden the Network and Remote Viewing Path
Many surveillance systems are connected to business networks for remote viewing and easier management. Segment the surveillance equipment onto its own network or VLAN so an office computer infection is less likely to reach cameras.
Reduce exposure to the open internet. Prefer a VPN or a secure remote access gateway rather than direct port forwarding to a recorder. Close unused services, keep firmware updated, and turn off features you do not need.
A well-designed system should make it easy for the right people to check cameras without creating easy openings for the wrong people. If you want a plain-language view of the value of video surveillance, focus on this: video helps most when it stays reliable and protected, and that reliability comes from both physical safeguards and strong cyber hygiene. When you protect uptime and access, you protect the usefulness of every clip you may need later.
Protect Power, Storage, and Evidence
A camera that loses power during an incident is a missed opportunity. Design your critical cameras and recorder with stable power and consider battery backup where outages or deliberate unplugging are realistic concerns.
Plan for storage resiliency. Use settings that balance quality and retention, and protect recordings from quick deletion. If your system supports it, consider write-protected evidence export procedures and restricted deletion rights.
Think like an investigator. Decide how footage will be preserved, who can export it, how it will be labeled, and where it will be stored. Consistent handling makes the video more useful if law enforcement, insurers, or attorneys become involved.
Set Up Monitoring, Response, and Recovery
Tampering is easier to stop when you notice it fast. Enable health checks and alerts for camera offline events, storage issues, and unusual login activity, then route those alerts to someone who will actually respond.
Write a short response plan. If a camera goes down, who checks it, how quickly, and what steps are allowed after hours? Security frameworks emphasize organizing actions across identifying issues, protecting systems, detecting problems, responding, and recovering.
Finally, practice recovery. Keep a basic spare kit such as mounts, weather covers, a spare camera for critical locations, and labeled cables. The goal is to restore coverage quickly without improvising in a stressful moment.
Train People and Audit the System Regularly
People are part of the system. Teach staff what normal camera placement looks like, how to spot lens obstruction, and how to report suspicious activity without assuming someone else will handle it.
Run quick monthly checks. Walk the site, confirm camera views are still correct, confirm time stamps are accurate, and review a few recorded clips for clarity. Small problems like a bumped angle or dirty lens are common and easy to fix early.
Do a deeper audit at least once a year. Review user accounts, confirm firmware update practices, re-check risk priorities, and verify that physical protections still match how your business operates.

Safeguarding business surveillance is mostly about protecting reliability. When cameras are placed thoughtfully, protected by layers, and supported by controlled access and a hardened network, tampering becomes harder, and failures become easier to catch.
Keep it simple: prioritize critical views, secure the recorder, segment the network, protect power and storage, and train staff to notice issues. Small, consistent habits often do more than complex upgrades that no one maintains.
Buy Me A Coffee
The Havok Journal seeks to serve as a voice of the Veteran and First Responder communities through a focus on current affairs and articles of interest to the public in general, and the veteran community in particular. We strive to offer timely, current, and informative content, with the occasional piece focused on entertainment. We are continually expanding and striving to improve the readers’ experience.
© 2026 The Havok Journal
The Havok Journal welcomes re-posting of our original content as long as it is done in compliance with our Terms of Use.